
The 5-Minute GPU Audit: A Checklist for Instantly Spotting Waste
Most organizations waste 95% of their GPU spend without knowing it. Run this five minute audit to find the leaks and fix them before the next invoice.
Perspectives, mises à jour et histoires de notre équipe

Most organizations waste 95% of their GPU spend without knowing it. Run this five minute audit to find the leaks and fix them before the next invoice.

The fix to platform team understaffing isn't hiring more — it's building on infrastructure where monitoring, security, and upgrades come built in.

Upstream contribution costs real engineering time. It also compounds over time in ways that internal fixes never do. What fifteen years of contributing to OpenStack, Kubernetes, and Ceph actually looks like.
Learn how to build zero-trust cloud infrastructure using OpenStack and Atmosphere. Discover security-by-default practices for enterprise private cloud in 2026.
The traditional "castle and moat" approach to security—where everything inside the network is trusted—is no longer viable. With distributed workloads, remote teams, and increasingly sophisticated threats, the perimeter has dissolved. In 2026, enterprises aren't asking if they should adopt zero-trust principles; they're asking how.
At VEXXHOST, security-by-default is a core investment priority this year (it has always been). We believe security shouldn't be an afterthought or an add-on—it should be baked into your cloud infrastructure from day one. In this post, we'll explore how to build zero-trust cloud infrastructure using OpenStack and our Atmosphere platform.
Zero-trust operates on a simple principle: never trust, always verify. Every user, device, and workload must continuously prove its identity and authorization—regardless of where it sits in your network.
The core tenets include:
For cloud infrastructure, this means rethinking how identity, networking, and access controls work together.
For a comprehensive framework on zero-trust principles, refer to , the foundational government standard for enterprise ZTA implementation.
Public cloud providers offer security tools, but implementing true zero-trust often means navigating a patchwork of services, proprietary configurations, and opaque networking layers. You're trusting the provider's implementation without full visibility.
Private cloud built on OpenStack offers distinct advantages:
You own every layer, from hypervisor to API endpoint. There's no black box. You can audit, customize, and harden each component to meet your specific threat model.
OpenStack's Neutron networking gives you complete visibility into traffic flows. You can implement micro-segmentation, define security groups with precision, and inspect east-west traffic that would be invisible in shared public cloud environments.
With private cloud, your data stays exactly where you mandate—critical for organizations navigating GDPR, HIPAA, SOC 2, or industry-specific regulations.
Multi-tenant public clouds introduce inherent risks. Side-channel attacks, noisy neighbors, and shared infrastructure vulnerabilities disappear when you control the hardware.
Atmosphere, our OpenStack-based cloud platform, is designed with security built into its foundation—not bolted on later. Here's how:
Authentication is the front door to zero-trust, and Atmosphere gives you enterprise-grade options out of the box:
OpenStack's native RBAC capabilities allow you to define granular permissions across projects, domains, and resources. Atmosphere makes it straightforward to implement least-privilege access:
Every interaction with your cloud happens through APIs. Atmosphere ensures:
Atmosphere leverages OpenStack Neutron to give you powerful network isolation:
Data at rest is protected through:
Implementing zero-trust isn't a single project—it's an ongoing practice. Here's a roadmap:
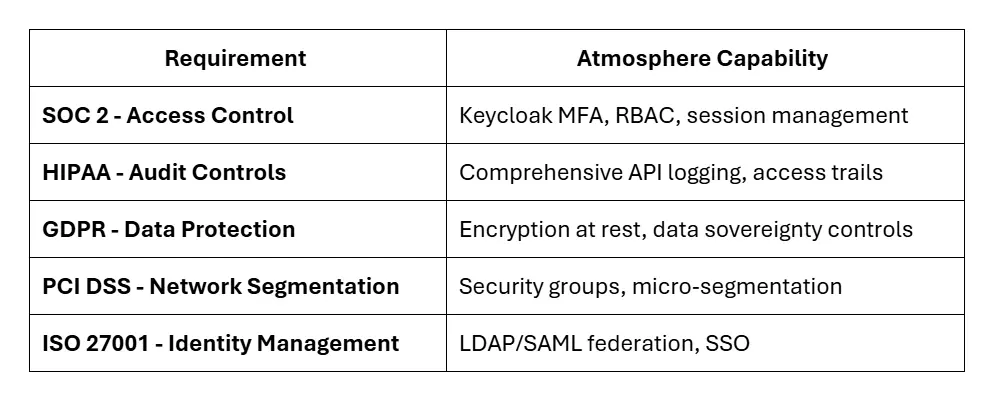
Zero-trust architecture isn't just good security practice—it's increasingly a compliance requirement. Atmosphere's security features map directly to common frameworks:
Security-by-default isn't about adding more tools—it's about building infrastructure where security is inherent, not incidental. With OpenStack's transparency and Atmosphere's integrated security capabilities, you can implement genuine zero-trust architecture without sacrificing operational efficiency.
At VEXXHOST, we're continuing to invest in advanced security tooling throughout 2026. Our goal is simple: make robust security the path of least resistance for your cloud deployment.
Ready to build zero-trust cloud infrastructure? Contact our team to learn how Atmosphere can help you implement security-by-default—or explore our security features in depth.
Choose from Atmosphere Cloud, Hosted, or On-Premise.
Simplify your cloud operations with our intuitive dashboard.
Run it yourself, tap our expert support, or opt for full remote operations.
Leverage Terraform, Ansible or APIs directly powered by OpenStack & Kubernetes